
Empowering Financial Decisions with a Student Loan Calculator
The Role of a Student Loan Calculator A student loan calculator is a powerful tool…





The Role of a Student Loan Calculator A student loan calculator is a powerful tool for students planning to fund higher education, helping manage costs like tuition, textbooks, and housing. By estimating monthly payments, total interest, and repayment periods for federal or private loans, it offers clear insights into borrowing needs. This tool enables students…

We are entering a new era when the most aesthetically breathtaking fusions of creativity and technology have only just started. In the past, the creative world relied heavily on costly materials and labor-intensive physical instruments. Digital identity and storytelling are currently being rethought in a very stylish and substantive way, owing to AI-powered visuals like…

When considering renewable energy solutions for home use, homeowners often find themselves comparing solar and wind power generators. Both options offer a sustainable way to reduce reliance on traditional power grids and decrease energy costs. However, solar power generators, such as the Jackery Solar Generator 2000 Plus, often emerge as the more suitable choice for…

Installing an air conditioning system may seem manageable for a determined DIYer. However, this seemingly straightforward task involves intricate technical details and potential risks that are often underestimated. Proper installation ensures energy efficiency, system longevity, and, most importantly, safety. If you’re tempted to take on an AC installation project, read on to understand why this…

Getting married is one of the biggest moments in the life of a person, and what better place to celebrate than Marbella! If you are planning a wedding in Marbella. The golden beaches, stunning, breathtaking views, beside the luxurious Mediterranean vibe make your special day worth celebrating there. This guide takes you through everything you…
Instagram has rapidly become one of the most powerful social media platforms, providing creators with the opportunity to reach millions of users across the globe. Whether you’re an aspiring influencer, a brand, or simply someone looking to make an impact, engagement is key to success on Instagram. Here are the best practices to maximise your…

Charge capture is about recording every service so that you can provide secure payment. It’s complicated and susceptible to errors. Charge capture to minimize billing errors typically includes data from multiple sources and systems that must be manually extracted, compiled, and reconciled. Additionally, it is reported that the Healthcare Financial Management Association states that healthcare…
Introduction Psychedelics have fascinated humanity for decades, offering profound experiences that challenge perception, creativity, and consciousness. One such psychedelic gaining popularity is 1P-LSD—a lesser-known but powerful compound that closely resembles LSD-25. But what exactly is 1P-LSD? How does it work, and why are so many people interested in it? In this in-depth guide, we’ll explore…

As the world shifts towards sustainable energy sources, solar energy stands out as a beacon of hope and innovation. With advancements in technology and increasing environmental awareness, solar energy is quickly becoming a cornerstone in the future of renewable energy. Here, we’ll explore why solar energy is pivotal for the future and introduce a powerful…
In today’s digital age, the demand for high-quality written content has surged exponentially. Whether you’re an entrepreneur looking to publish a book, a business executive seeking to establish thought leadership, or a content creator requiring consistent material, finding the right ghostwriter can be crucial to your success. This comprehensive guide explores how to find and…
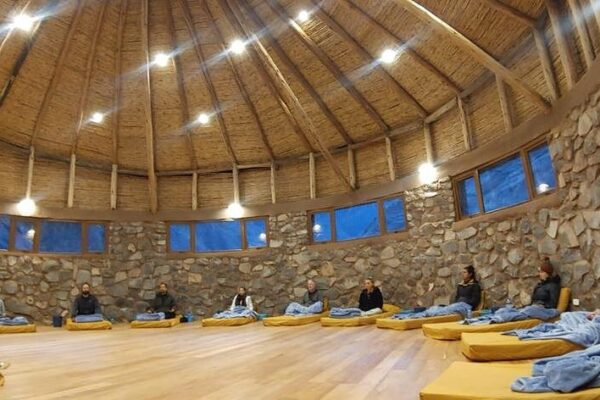
Embark on a journey of profound transformation at an Ayahuasca retreat in Ecuador, where ancient traditions meet modern healing practices. Nestled in the heart of nature, these retreats offer a safe and sacred space for spiritual growth, emotional healing, and self-discovery. For those seeking to unlock their potential or overcome personal struggles, Ecuador is a…

Metaphysical science, often associated with the exploration of spirituality, consciousness, and the deeper aspects of reality, offer profound insights that can transform your life. By embracing the principles of metaphysical teachings, individuals can enhance their personal growth, improve their well-being, and create a more harmonious existence. In this article, we’ll delve into how metaphysical sciences…